Optimize Your Firewall: Essential Settings for Comprehensive Network Security
In today's interconnected world, a robust firewall is the cornerstone of digital defense for individuals and organizations alike. It acts as a digital gatekeeper, monitoring and controlling incoming and outgoing network traffic based on predefined security rules. The stakes are incredibly high; a compromised network can lead to data breaches, financial losses, and significant reputational damage. When we consider the value of digital assets and the security protecting them, thoughts naturally turn to the immense worth of impenetrable defenses. This often prompts questions about the financial implications or the perceived "net worth" of cutting-edge security, perhaps even leading to queries like "the firewall jon rekon net worth." While specific individuals' financial details are beyond the scope of general cybersecurity advice, the underlying sentiment highlights a crucial truth: the true 'net worth' of a secure firewall lies in its unparalleled ability to safeguard the invaluable digital assets, privacy, and operational continuity of any entity it protects.
Optimizing your firewall settings isn't a one-time task but an ongoing commitment to vigilance. This article will delve into essential configurations and strategies to fortify your network's perimeter, ensuring your digital environment remains resilient against evolving threats.
Understanding the Core Function and Importance of Your Firewall
At its heart, a firewall is a network security device that monitors and filters incoming and outgoing network traffic based on an organization's previously established security policies. It creates a barrier between a trusted internal network and untrusted external networks, suchifying the Internet. Modern firewalls, particularly stateful inspection firewalls, go beyond simple packet filtering. They can track the state of active connections, ensuring that only legitimate responses to outgoing requests are allowed back in, significantly enhancing security.
The importance of this function cannot be overstated. Without a properly configured firewall, your network is an open target for a myriad of threats, including:
- Malware and Viruses: Preventing malicious software from entering your network.
- Hacking Attempts: Blocking unauthorized access to your systems.
- Data Theft: Protecting sensitive information from being exfiltrated.
- DDoS Attacks: Mitigating denial-of-service attempts that can cripple operations.
- Unwanted Access: Controlling which applications and users can access the internet or your internal network.
For home users, the firewall integrated into your router or operating system (like Windows Firewall or macOS Firewall) is your primary defense. For businesses, dedicated hardware firewalls or next-generation firewalls (NGFWs) offer more advanced features, including intrusion prevention, application control, and deep packet inspection. Regardless of the type, the principle remains: proper configuration is paramount to its effectiveness.
Key Firewall Settings for Optimal Protection
Configuring your firewall effectively requires a balance between security and functionality. Overly restrictive settings can hinder legitimate operations, while lax settings leave you vulnerable. Here are essential settings to optimize for robust protection:
1. Implement a "Deny-All" Inbound Policy
This is arguably the most fundamental and critical setting. Your firewall should, by default, block all incoming connections unless explicitly allowed by a specific rule. This "default deny" posture dramatically reduces the attack surface by ensuring that only necessary services and applications are exposed to the external network. Conversely, an "allow-all" policy (common in many default home router configurations for outbound traffic) should be carefully reviewed and tightened if unnecessary outbound connections need to be restricted.
2. Meticulous Port Management and Forwarding
Ports are communication endpoints for network services. Many common services use well-known ports (e.g., HTTP on port 80, HTTPS on port 443, SSH on port 22). To minimize exposure:
- Close Unnecessary Ports: Audit your network for open ports and close any that are not actively used by legitimate services. Every open port is a potential entry point for an attacker.
- Limit Port Forwarding: If you need to access an internal service from outside your network (e.g., a home server), use port forwarding. However, apply it sparingly. Forward only the specific ports required, and ideally, map external high-numbered, non-standard ports to internal standard ports for an added layer of obscurity (though this is not a true security measure). Always specify the exact internal IP address, never broadcast.
- Consider VPN for Remote Access: Instead of opening ports for services like RDP or SSH directly to the internet, establish a Virtual Private Network (VPN) connection first. This encrypts your traffic and tunnels it securely into your network, bypassing the need for open ports.
3. Smart Rule Prioritization and Granularity
Firewall rules are processed in a specific order, usually from top to bottom. More specific rules should generally come before broader, more general rules. For example, a rule to "deny access from a specific malicious IP address" should be higher than a rule to "allow all HTTP traffic." Furthermore, rules should be as granular as possible, specifying source IP, destination IP, port, and protocol to minimize unintended allowances.
4. Enable and Regularly Review Logging
Your firewall generates logs of its activity, including blocked connection attempts, allowed traffic, and system events. Enabling comprehensive logging is vital for security auditing and incident response. Regularly reviewing these logs can help you identify suspicious activity, misconfigured rules, or even successful attacks. Tools like OpenWrt provide detailed logging capabilities, which, when properly interpreted, offer invaluable insights into network behavior and potential threats. To learn more about how to make sense of these records, refer to our article on Decoding OpenWrt Firewall Logs for Network Insights.
Actionable Tip: Set up alerts for critical events, such as multiple failed login attempts or connections from known malicious IP ranges. Consider sending logs to a centralized syslog server for easier management and analysis, especially in larger environments.
5. Regular Firmware and Software Updates
Firewall software and firmware updates often include patches for newly discovered vulnerabilities. Running outdated software leaves your firewall exposed to known exploits. Make it a habit to check for and apply updates promptly.
Advanced Firewall Strategies and Open-Source Solutions
Beyond the fundamental settings, advanced strategies and the adoption of open-source solutions like OpenWrt can significantly enhance your network's resilience.
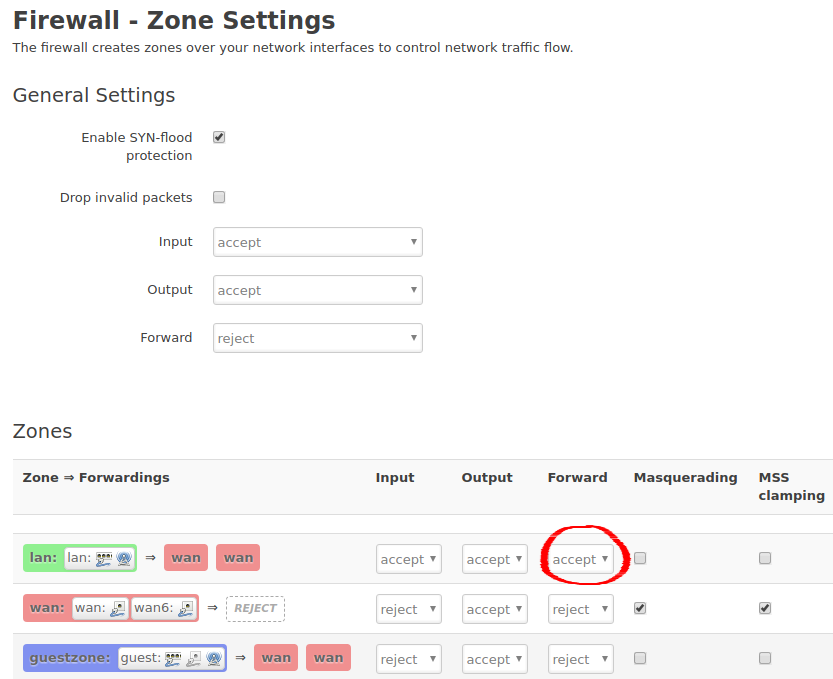
Leveraging OpenWrt for Enhanced Control
OpenWrt is a Linux-based operating system for embedded devices, primarily routers. Its strength lies in providing unparalleled flexibility and control over network functions, including the firewall. OpenWrt uses iptables (or nftables in newer versions) as its underlying firewall engine, managed through a powerful web interface called LuCI (which itself depends on the luci-app-firewall package for its firewall configuration capabilities). This dependency highlights the tightly integrated nature of OpenWrt's components, allowing users to craft highly customized and granular firewall rules.
With OpenWrt, you can implement advanced features like:
- Intrusion Detection/Prevention Systems (IDS/IPS): Integrate packages like Snort or Suricata to detect and potentially block malicious traffic patterns.
- Geo-blocking: Block traffic to and from entire countries or geographical regions known for high rates of cybercrime.
- Traffic Shaping and QoS: Prioritize critical network traffic while de-prioritizing less important data.
- VPN Server/Client: Easily set up a VPN server to securely access your network remotely or configure your router to connect to a VPN service.
Understanding OpenWrt's core dependencies, such as LuCI's reliance on luci-app-firewall, is crucial for effective management and troubleshooting. Dive deeper into these architectural aspects with our guide on OpenWrt Firewall Dependencies: Understanding LuCI's Core.
Layered Security Approach
A firewall is a critical component, but it should not be your only defense. Employ a layered security approach that includes:
- Antivirus/Anti-Malware: On all endpoints.
- Endpoint Detection and Response (EDR): For advanced threat hunting on devices.
- Strong Authentication: Multi-factor authentication (MFA) everywhere possible.
- Regular Backups: To recover from data loss or ransomware attacks.
- Employee Training: To educate users about phishing and social engineering.
The True "Net Worth" of a Secure Firewall
While the immediate cost of a firewall solution can range from free (software-based) to thousands of dollars (enterprise-grade hardware), its true value – its "net worth" – is immeasurable. A well-configured firewall protects against financial losses from fraud and data breaches, preserves brand reputation, ensures business continuity, and safeguards personal privacy. It's an investment that pays dividends by averting the catastrophic consequences of a successful cyberattack. Thinking about the firewall jon rekon net worth in abstract terms leads us to the broader understanding that strong cybersecurity is a non-negotiable asset for anyone operating in the digital realm. The peace of mind and operational stability it provides far outweigh the cost and effort of its implementation and ongoing maintenance.
Conclusion
Optimizing your firewall settings is an ongoing, essential process for anyone connected to the internet. By implementing a deny-all inbound policy, meticulously managing ports, prioritizing rules, enabling comprehensive logging, and keeping your systems updated, you build a strong foundation for network security. Leveraging powerful open-source solutions like OpenWrt can provide even greater control and advanced defensive capabilities. Remember that the digital landscape is constantly evolving, so regular audits, continuous learning, and a proactive stance are key to maintaining a secure and resilient network. Invest in your firewall; it's an investment in your digital future.